SAP Security
What Is Security?
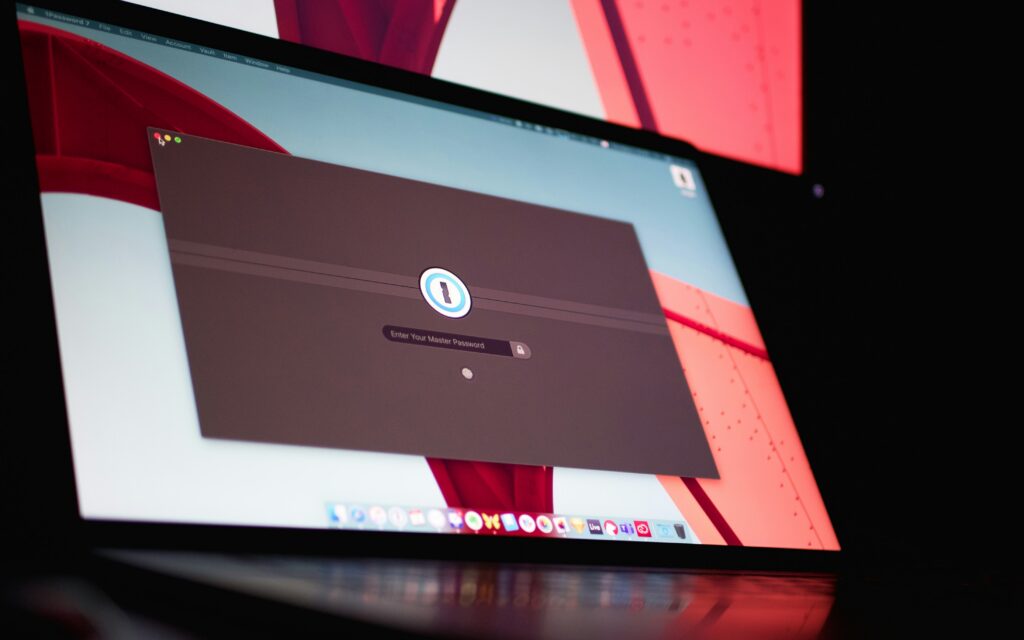
Security is a broad term that can apply to many fields. In the area of IT, security refers to tools and strategies that prevent unauthorized access to organizational assets such as computers, networks, and data. Security is designed to maintain the integrity and confidentiality of sensitive information, blocking the access of sophisticated hackers and malicious insiders.
What Is Security?
Security is a broad term that can apply to many fields. In the area of IT, security refers to tools and strategies that prevent unauthorized access to organizational assets such as computers, networks, and data. Security is designed to maintain the integrity and confidentiality of sensitive information, blocking the access of sophisticated hackers and malicious insiders.
What Is SAP Security?
SAP security products and services help organizations to develop and administer solutions securely across on-premise, cloud, and hybrid environments. The SAP Trust Center includes links to various SAP security tools and services under five categories:
- Hybrid identity and access management: SAP Single Sign-On, SAP Identity Management, and SAP Access Control.
- Cloud identity services: SAP Cloud Identity Services – Identity Authentication, SAP Cloud Identity Services – Identity Provisioning.
- Secure development services: SAP Authorization and Trust Management service, SAP Credential Store, Cloud Connectors, and SAP Cloud Programming Model.
- Risk and compliance: SAP Cloud Identity Access Governance, SAP Data Retention Manager, SAP Customer Data Cloud, and SAP Data Privacy Integration.
- Security support services: SAP Security Optimization, SAP MaxAttention, and Security Service and Support Offerings.
Further Resources for SAPinsiders
Trust Matters! The SAP Security Strategy and Roadmap. This presentation by Anne Marie Colombo, Cybersecurity Solution Advisor at SAP, provides an overview of SAP’s security strategy as well as its related solutions and products. The presentation explains how the latest solutions and services, such as SAP Cloud Platform Identity Authentication, SAP Cloud Platform Identity Provisioning, SAP Enterprise Threat Detection, SAP Single Sign-On, and SAP Identity Management, can bring value to your enterprise security platform.
Insights for Your Emerging SAP Security Strategy. In this blog post, SAPinsider discusses security with key leadership from SAP security company Onapsis. The discussion ranges across many topics, from the state of SAP software and enterprise security to Onapsis’s acquisition of Virtual Forge and its impact on the SAP customer base.
Application Security Imperiled by Attackers. Application security is being threatened by cyberattacks on the application layer, such as SAP S/4HANA systems, which target valuable resources organizations store there, observe SAP’s Arndt Lingscheid, Global Solution Owner Cybersecurity and Data Protection, and Martin Mueller, Presales and Program Manager, SAP Security Suite. Companies need to deploy real-time detection and response to deal with the rise in attacks against the SAP application layer level, they argue.
Vendors that can help SAP customers with security include: Appsian Security, Fastpath, Fortinet, Layer Seven Security, Lookout, Onapsis, Security Weaver, Xiting, and Xpandion.