Back to Vendor Directory
Onapsis
Onapsis is the global leader in SAP cybersecurity and compliance, trusted by the world’s leading organizations to securely accelerate their SAP cloud digital transformations with confidence. As the SAP-endorsed and most widely used solution to protect SAP, the Onapsis Platform empowers Cybersecurity and SAP teams with automated compliance, vulnerability management, threat detection, and secure development for their RISE with SAP, S/4HANA Cloud and hybrid SAP applications.
![]()
Featured Solutions
The modern threat landscape requires a unified defense. While traditional SIEM tools provide broad infrastructure coverage, they often lack the depth required to monitor the SAP application layer.
The Onapsis Agentic Gateway unlocks agentic AI SAP Cybersecurity workflows, transforming the Onapsis Platform into a central nervous system for autonomous SAP risk management and cross-functional AI orchestration.
Featured Content
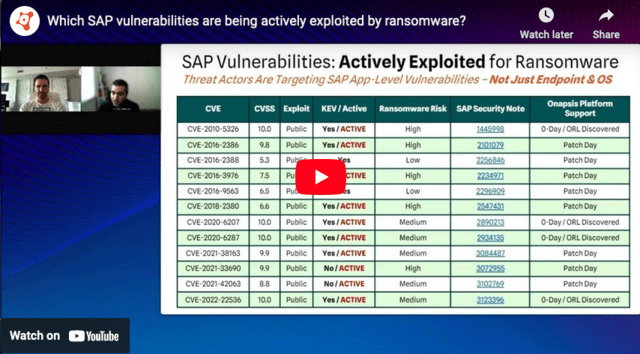
The era of "patch and pray" is officially over — in 2025, attackers weaponized SAP zero-days within hours of disclosure, deploying ransomware before most organizations had even opened the security note. Discover how leading enterprises are fighting back with SAP Threat Intelligence: a dynamic, AI-aware defense strategy that breaks the silos keeping your ERP blind spots hidden from your SOC.
We partnered with SAP Press to deliver the definitive guide to Cybersecurity for SAP
Multimedia Center
Join cybersecurity leaders from EclecticIQ, Mandiant, NightDragon, and Onapsis as they dissect the recent wave of SAP zero-day attacks and provide proactive defense strategies.
In this webinar, learn how enhanced visibility, automated security scanning, and incident response can augment your team’s ability to inspect what they expect from RISE with SAP, increase business value, and promote risk abatement.
Articles / Case Studies / Videos
SAPinsider Research Webinar- Technology Leader’s Strategic Agenda for 2026Watch this on-demand SAPinsider webinar and learn how our latest benchmark research translates into practical guidance for technology leaders navigating ERP optimization, AI adoption, cost pressures, and business alignment in 2026.
Technology leaders are entering 2026 under pressure to do two things at once: improve efficiency and control costs while still enabling innovation, new growth, and stronger data-driven decision making. SAPinsider’s latest research shows that these priorities are shaping everything from ERP roadmaps to automation, analytics, and AI strategies, making it critical for technology leaders to connect business outcomes with the SAP investments they make next.
In this on-demand webinar, SAPinsider experts unpack what the data means in practice. You will hear why optimization of existing SAP S/4HANA environments is emerging as the leading SAP initiative, why SAP BTP is drawing the strongest investment interest beyond core ERP, and how organizations are approaching AI in SAP even though many are still early in adoption. The session also examines the persistent challenges of aligning IT and business stakeholders, managing cost pressure during transformation, and responding to macroeconomic and geopolitical disruption without losing momentum on strategic priorities.
What you will gain from the session:
- Understand the top business and SAP priorities for 2026, including the strong emphasis on operational efficiency, cost reduction, revenue growth, and better decision making.
- See how leading organizations are balancing optimization of SAP S/4HANA with newer investments in SAP BTP, analytics modernization, process automation, and cloud ERP strategy.
- Learn where AI in SAP is gaining traction, which use cases are being prioritized first, and what is holding many organizations back from broader adoption.
- Hear how technology leaders are addressing the real-world obstacles that continue to challenge execution, from stakeholder alignment and budget pressure to skills gaps and ROI concerns.
- Get practical perspective on how global uncertainty, regulatory change, and cost pressure may reshape SAP roadmaps over the rest of 2026 and into 2027.
Watch the webinar on demand to learn how peers are prioritizing SAP S/4HANA optimization, BTP investments, analytics modernization, and AI-enabled transformation in the year ahead.
Apr 14, 2026
Establishing a Strategic Mandate: How JYSK Automated SAP Security and Outpaced Industry Maturity BenchmarksOperating 3,600+ stores across 50 countries, JYSK needed SAP security that could match the scale and complexity of their global retail operations — without slowing down innovation. By partnering with Onapsis, they didn't just solve today's challenges; they built a governance-driven security foundation that now outpaces their entire industry on maturity benchmarks.
Apr 16, 2026
Leading Automotive Manufacturer, Škoda, Secure-by-Design Approach Improved Performance of ERP Systems While Saving TimeWhen standard market tools failed to meet Škoda's rigorous code quality and compliance requirements, the leading automotive manufacturer turned to Onapsis to bring order to their complex SAP landscape. The result was a proactive, continuous quality assurance engine that not only slashed critical incidents and manual review effort, but elevated Škoda to a security benchmark within one of the world's largest automotive groups.
Apr 16, 2026
How a Global Apparel Manufacturer Secured Its First SAP Cloud MigrationA global apparel manufacturer successfully implemented an SAP HANA Enterprise Cloud system with Onapsis' platform to ensure visibility, continuous risk monitoring, and adherence to security standards, allowing for secure operations and minimization of disruptions in their supply chain.
Apr 16, 2026
Fortune 500 Utility Company Partners with Onapsis to Build Security into Their RISE with SAP Transformation and Achieve Secure, On-Time, On-Budget Go-LiveA Fortune 500 utility company, facing challenges with their legacy SAP system, chose the RISE with SAP program for a clean migration to SAP S/4HANA, recognizing the need for enhanced security skills and expertise, and found a trusted partner in Onapsis to provide the necessary support and technology for their transition.
Apr 3, 2025
The Dangers of AI in Custom Code: How to Secure Your SAP LandscapeThe rapid evolution of AI in software development significantly increases efficiency while simultaneously introducing severe security risks, necessitating a proactive, automated Application Security Testing strategy to effectively manage vulnerabilities in custom code.
Apr 16, 2026
Mythos & GPT-5.4-Cyber: The Upcoming AI-Driven “Vulnerability Surge” in SAPFrontier AI models like Claude Mythos and GPT-5.4-Cyber enable the autonomous discovery of zero-day vulnerabilities, necessitating a proactive industry response to cybersecurity with integrated defenses in organizations' core operations to address the rising threat landscape.
Apr 16, 2026
Webinar: The State of SAP Security: 2025 Vulnerabilities, Exploits & Lessons LearnedThe webinar recaps significant SAP security vulnerabilities from 2025 and offers tailored guidance for enhancing defenses in 2026, including insights on specific exploits and a checklist for securing SAP landscapes.
Apr 16, 2026
The SAP Shared Responsibility Model: Who Secures What in the Cloud Era?SAP has initiated a monthly Security Patch Day to address vulnerabilities through SAP Security Notes, while highlighting the importance of the Shared Responsibility Model in cloud environments, which delineates security obligations between the provider and the customer, particularly as organizations migrate to cloud-based SAP solutions.
Apr 16, 2026
2026 SAP Security ChecklistThe datasheet provides a comprehensive SAP security checklist for 2026, focusing on critical areas such as platform hardening, vulnerability management, access controls, incident response, compliance, cloud security, and necessary skills, aimed at helping organizations mitigate emerging threats as they utilize increasingly complex SAP environments.
Apr 16, 2026
The Beginners Guide for Digital Transformation with S/4HANAWith the 2027 SAP ECC end-of-support deadline fast approaching, organizations face a critical choice: migrate to S/4HANA with a clear security strategy, or risk carrying legacy vulnerabilities, compliance gaps, and costly technical debt into their most business-critical environment. This beginner's guide breaks down every stage of the transformation journey — from planning and custom code assessment to go-live and beyond — so your organization can move fast without leaving security behind.
Apr 16, 2026
Secure Your Systems with Effective Vulnerability ManagementThis article discusses the significance of vulnerability management for critical business applications like SAP and Oracle, highlighting common vulnerabilities such as missing patches, misconfigurations, and authorization issues, and emphasizes the need for prioritization and efficient remediation processes in an increasingly digitized and risk-prone environment.
Apr 16, 2026
Application Security Testing Best PracticesFor CISOs and CIOs tasked with protecting business-critical SAP applications, a patchwork of manual code reviews and reactive vulnerability fixes is no longer a viable security strategy. Discover how embedding automated, end-to-end application security testing directly into your SAP development lifecycle can dramatically reduce risk, cut costly production errors, and give your security team the visibility they need to stay ahead of attackers.
Apr 16, 2026
The Ultimate Guide for SAP Enterprise Threat DetectionSAP Enterprise Threat Detection (SAP ETD) is a comprehensive cybersecurity solution designed to enhance the security of SAP landscapes by providing real-time monitoring and advanced threat detection capabilities, ensuring the protection of critical business data against evolving cyber threats.
Apr 16, 2026
What is SAP GRC?: Governance, Risk, and Compliance in the Modern EnterpriseIn the context of increasing digital transformation, robust Governance, Risk, and Compliance (GRC) processes within SAP environments have become essential for organizational resilience, enabling informed decision-making, operational efficiency, and protection against risks like fraud and regulatory penalties.
Apr 16, 2026
Code Vulnerability Analysis for SAPAs SAP applications become the backbone of global enterprise operations, a single undetected line of vulnerable custom code can open the door to data breaches, ransomware, and full system compromise. Learn how to shift left with automated static code analysis and continuous vulnerability scanning — and why building security into every stage of the SAP development lifecycle is the only sustainable defense in today's threat landscape.
Apr 16, 2026
Navigating Security Challenges with SAP RISESAP RISE is a comprehensive Business Transformation as a Service (BTaaS) solution that facilitates seamless migration to the SAP cloud ecosystem, enhances operational efficiency through modular components such as SAP S/4HANA Cloud and SAP Business Technology Platform, and emphasizes the importance of robust security measures throughout the digital transformation journey.
Apr 16, 2026
Why Security Timing Determines Success in RISE with SAP TransformationsSecurity timing often determines whether RISE with SAP transformations stay on track. This analysis examines how late risk discovery undermines migration, execution, and post–go-live outcomes, and why secure-by-design approaches change delivery discipline.
Feb 2, 2026
SAP Cloud Security: Best Practices to Safeguard Your Cloud-Based SAP SystemsAs enterprises race to migrate SAP workloads to the cloud, a dangerous misconception is leaving critical systems exposed: that SAP's built-in protections are enough. Discover how to close the visibility gap, master the shared responsibility model, and build a cloud security strategy that keeps your most business-critical SAP applications protected — from misconfigurations and insider threats to regulatory compliance and beyond.
Apr 16, 2026
SAPinsider Benchmark Research – Technology Leader’s Strategic Agenda for 2026Technology leaders in the SAP space must balance the need to continuously innovate and remain current on SAP solutions and technology while supporting the needs of business teams and achieving organizational goals. In 2026, these leaders face significant challenges. Geopolitical instability and global macroeconomic uncertainty must be weighed against the need to complete and optimize ERP transformations, deploy AI within SAP applications, and manage costs effectively. This can make supporting business priorities while driving innovation a challenge that should be explored and understood.
To understand the strategic agenda for technology leaders in 2026, SAPinsider surveyed its community between December 2025 and March 2026 to identify their key priorities for 2026, what they are doing to support business goals, the biggest challenges they are facing as a technology leader, their SAP priorities and planned investments, the status of their ERP journey, and their planned use of AI in SAP-related initiatives. Additionally, respondents were also asked about the global factors they expect will impact their strategies in 2026.
Not surprisingly, increasing operational efficiency and reducing costs were identified by 70% of respondents as their top priority. Managing costs has long been important for technology leaders, even as they strive to implement technologies that support new or changed business requirements. While it is not always possible to manage costs, it may be more possible to increase the efficiency of existing processes, which can, in turn, bring cost savings. Technologies that help achieve these goals are crucial from a business priorities standpoint.
Download the benchmark report to read the full data analysis and receive recommendations for your own plans.
- Discover why foundational investments in SAP BTP are currently outpacing direct spending on artificial intelligence.
- Learn how macroeconomic volatility and geopolitical tensions are actively forcing IT leaders to restructure their SAP roadmaps.
- Understand the critical danger of deprioritizing cybersecurity during rapid ERP transformations and AI deployments.
Mar 31, 2026
Automating DevSecOps to Better Secure SAP SystemsThe rise of cyber threats targeting ERP systems necessitates an urgent shift towards integrated security within SAP development processes, as Onapsis updates its platform to enhance code security, transport governance, and runtime protection for enterprise resilience.
Dec 31, 2025
10 Critical Questions to Ask Your SAP Security VendorChoosing the right SAP security partner is crucial as generic cybersecurity tools fail to secure vital applications, so it's essential to assess if a vendor provides comprehensive, research-driven protection against sophisticated threats through targeted questions.
Apr 16, 2026
SAPinsider Benchmark Research – RISE with SAP 2025As 2025 ends, the narrative around SAP migration has shifted from “why move?” to “how fast?”
This SAPinsider report, based on a survey of 122 community members conducted in late 2025, highlights a marked acceleration in cloud ERP adoption as the 2027 end-of-maintenance deadline approaches.
Now commercially referred to as SAP Cloud ERP Private, the RISE with SAP package is seeing varied adoption rates; smaller organizations (under $2 billion in revenue) are currently twice as likely to be live on the solution compared to larger enterprises, which are predominantly in the planning or exploration phases.
While SAP’s dedicated transition support and license conversion credits are the primary drivers for migration, cost and unclear business value remain significant barriers for holdouts. The report also identifies a growing influence of Generative AI on ERP strategy. However, it warns of critical gaps in security compliance and an impending shortage of skilled implementation resources.
Download the benchmark report to read the full data analysis and receive recommendations for your own plans.
- Understand why there is a concerning lack of security awareness
- Why we forecast that implementation partners will struggle to staff the volume of concurrent projects required to meet the 2027 and 2030 deadlines.
- How SAP’s direct support and financial incentives are driving adoption rates
Nov 26, 2025
Reviewing Zero-Day Vulnerabilities in SAPIn March 2025, cybersecurity firms detected exploitation activities linked to a critical zero-day vulnerability in SAP NetWeaver, leading to a swift patch by SAP, but many organizations had already suffered significant impacts, emphasizing the urgent need for improved visibility, auditing, and responsiveness in securing SAP systems.
Nov 19, 2025
Onapsis and Microsoft Partner to Provide End-to-End SAP Security MonitoringOnapsis has launched an integration between Onapsis Defend and Microsoft's Sentinel SIEM platform to enhance threat detection and response for SAP applications, addressing security challenges by providing SOCs with unified visibility and enriched threat intelligence.
Nov 12, 2025
New Onapsis Platform Updates Deliver Deeper SAP SecurityAs SAP systems face increasing cyber threats, Onapsis has announced new functionality in its platform to enhance security and patch management, emphasizing the importance of prioritizing SAP protection, securing executive support for cybersecurity initiatives, and adopting a layered defense strategy.
Sep 25, 2025
SAPinsider Benchmark Research Webinar – RISE with SAP 2025A Market Divided and a Looming Resource Crunch
Organizations are facing a pivotal moment as the shift to SAP Cloud ERP accelerates and the end of maintenance for core SAP ERP systems nears. SAPinsider’s latest RISE with SAP Benchmark Research reveals how companies are responding to rising pressure to modernize, the reasons behind their adoption decisions, and the challenges they must overcome. With two thirds of respondents already running, deploying, or exploring SAP Cloud ERP, the findings offer an in-depth look at what is driving ERP transformation in 2025 and where organizations are investing to prepare for the future.
In this session, SAPinsider analysts walk through the key data shaping cloud ERP strategy, including the role played by SAP Cloud ERP Private (RISE with SAP), the impact of AI capabilities such as Joule, and the realities of skills shortages, security requirements, and cost considerations. Attendees will gain a research-driven view of how peers are planning, executing, and governing their transitions, along with practical insights they can use to guide their own ERP roadmaps.
Watch this session to:
- Understand what is driving organizations to accelerate their move to SAP Cloud ERP Private and how adoption differs by company size.
- Learn why support from SAP, access to new functionality, and the rise of generative AI are shaping decision making.
- Hear which challenges organizations say are most difficult, including data cleansing, custom code remediation, and securing business support.
- See how companies are forming strategy teams, involving executives, and preparing for resource shortages in the coming years.
- Gain guidance on the steps organizations should take now to prepare for ERP transformation and long term innovation.
Dec 5, 2025
Critical SAP Zero-Day Vulnerability Under Active ExploitationActive exploitation of a critical zero-day vulnerability (CVE-2025-31324) in the SAP Visual Composer component allows unauthenticated attackers to gain full control over SAP systems, prompting SAP to release an emergency patch and urging customers to either apply it or disable access to the vulnerable component.
Apr 30, 2025
Understanding Threat Actors Attacking SAP with OnapsisIn April 2024, Onapsis, in collaboration with Flashpoint, released the 'Ch4tter: Threat Actors Attacking SAP for Profit' report, emphasizing the evolving cybersecurity risks facing SAP organizations and advocating for proactive measures like penetration testing and ongoing education to mitigate these threats.
Apr 22, 2025
Beyond Patching: Building a Multi-Layered Defense for Your SAP LandscapeThis whitepaper provides SAP users and CISOs with best practices for securing SAP systems, emphasizing the importance of a multi-layered defense strategy that goes beyond traditional patching. It offers insights into the multifaceted aspects of SAP cybersecurity to help organizations protect their critical SAP landscapes.
Apr 11, 2025
Ensuring Security is at the Heart of a Clean Core StrategyAs companies transition to SAP S/4HANA under the Clean Core strategy to streamline operations and reduce legacy complexity, they must also navigate new security challenges associated with increased customization and cloud integrations, prompting collaboration with security partners like Onapsis to maintain a secure and efficient environment.
Jun 23, 2025
Onapsis Announces New Cybersecurity Book to Debut at SAPinsider Vegas 2025At SAPinsider Vegas, technology leaders will gather to explore SAP landscape optimization and cybersecurity, highlighted by the release of Onapsis's new book 'Cybersecurity for SAP,' co-authored by its CTO and focused on addressing security challenges amid rising cyber threats.
Mar 17, 2025
From Discovery to Defense – Securing SAP with OnapsisMariano Nunez transformed his passion for cybersecurity into leadership at Onapsis, a company he founded to enhance SAP security against evolving cyber threats, emphasizing the necessity of proactive measures and collaborative frameworks as organizations migrate to the cloud.
Mar 14, 2025
Onapsis Announces New Secure RISE AcceleratorOnapsis has launched the Secure RISE Accelerator to enhance cybersecurity and compliance during RISE with SAP transformations by automating processes, conducting risk assessments, and providing expert support, thus enabling organizations to innovate securely and efficiently.
Nov 19, 2024
Bolstering Cybersecurity and Resilience with OnapsisAs the average cost of an SAP data breach rises to $10 million, organizations must enhance their cybersecurity strategies by focusing on technology, processes, and skilled personnel, while leveraging RISE with SAP along with Onapsis to effectively manage cloud security risks.
Jan 16, 2025
Onapsis Announces Security Testing Solution: Control CentralOnapsis has launched Control Central, a new product within its Control suite that enhances application security testing for RISE with SAP transformations by automating code scanning, reducing manual tasks, and aiding organizations in securing their SAP environments against vulnerabilities.
Feb 6, 2025
Onapsis Announces Enhanced Security Features for SAP BTPThe SAP cybersecurity specialists at Onapsis announced that they have expanded their Control product line to feature a bundle that bolsters the security of SAP Business Technology Platform (BTP). This new solution allows users to automatically scan code for potential threats throughout a number of environments and depositories. The product is available as of Q4 […]
Dec 4, 2024
Securing SAP Remote Function Calls: The Crucial Role of S_ICF AuthorizationThe article discusses the importance of the S_ICF authorization object in SAP systems as a security measure to mitigate RFC hopping attacks by controlling access to RFC destinations and ensuring that only authorized users can initiate function calls, thereby reducing the risk of unauthorized privilege escalation following a cyber attack.
Sep 23, 2024
Hash Cracking and the SAP LandscapeThis article discusses the use of hashing for password security in SAP systems, explaining how hashes are stored, methods for cracking them using tools like JohnTheRipper and Hashcat, and emphasizes the importance of addressing weak hashes and deactivating downward compatibility to enhance data protection.
Sep 23, 2024
83% of Organizations experienced at least one ransomware attack in the last yearA recent report reveals that 83% of organizations faced ransomware attacks in the past year, with significant impacts on ERP systems, prompting 93% to seek dedicated ERP security solutions, while concerns grow over AI-enhanced threats and organizations increasingly adjusting their cybersecurity strategies and investments.
Sep 23, 2024
ERP Security for Utility Companies – Onapsis Partners with SNOPUD to Secure Critical SAP ApplicationsCyberattacks on utility companies are increasingly targeting vulnerabilities in SAP applications, posing significant financial and operational risks, with the average cost of a data breach reaching $4.72 million. The energy sector, with its sensitive enterprise resource planning (ERP) systems like SAP, is particularly attractive to cybercriminals. Despite this, many utility companies struggle to allocate adequate resources for security, especially amid ongoing digital transformation efforts. The consequences of such attacks can be severe, leading to business disruptions, power or water outages, and the theft of customer data. To address these challenges, Onapsis, a leader in business application security, has partnered with Snohomish County Public Utility District (SNOPUD) to enhance SAP security through its Connect Up initiative, aimed at upgrading meters across homes and businesses. This collaboration leverages Onapsis' threat intelligence and automated vulnerability remediation to safeguard SNOPUD's critical systems and customer data, supporting a security-first approach as the utility modernizes its operations.
Aug 14, 2024
Augmenting Existing SAP Network Security with OnapsisA recent study by Onapsis highlights a 400% rise in ransomware incidents targeting SAP systems, emphasizing the critical need for enhanced security measures to protect these applications. SAP offers various security features, including user authentication, encryption, and monitoring controls like SAProuter. However, if compromised, SAProuter can be an entry point for unauthorized access. Traditional vulnerability management and security monitoring often fall short for SAP systems, leading to a lack of visibility and effective threat detection. Onapsis addresses this gap with its automation capabilities and in-depth threat intelligence from Onapsis Research Labs. Key Solutions offered by Onapsis include Onapsis Assess that supports SAProuter, extending vulnerability management with automated scans and risk-driven analysis. This enables better prioritization and faster response to potential threats without manual intervention. Similarly, Onapsis Defend continuously monitors SAProuter for insider threats and potential compromises. It swiftly detects unauthorized access through targeted alerts and monitors over 2,000 threat indicators, including zero-day threats.
The Onapsis Platform operates independently of SAP systems, ensuring security without compromising performance. It offers visibility into critical SAP systems, helping teams manage security, compliance, and availability issues through advanced analytics, reporting, and automation tools.
Jul 16, 2024
Vulnerabilities Affecting SAP AI ServicesOn July 17th, 2024, Hillai Ben-Sasson, a security researcher from the cloud company WIZ released the results of a research focused on SAP Cloud AI services, which was part of a broader research around mainstream AI cloud providers also including Hugging Face and Replicate. The researcher identified a set of weaknesses in the cloud infrastructure of the SAP Core AI service.
Aug 13, 2024
Lessons from Onapsis-Flashpoint Report and BeyondIn the realm of enterprise resource planning (ERP) systems, security is a constant battleground. Despite the availability of patches for known vulnerabilities, the Onapsis-Flashpoint Ch4tter report sheds light on a worrying trend: increased attack activities on these critical systems.
Aug 13, 2024
Protecting SAP Solutions from Cyber Threats with OnapsisRecent SAPinsider research highlights that protecting sensitive data in SAP systems is a major concern for SAP customers. Traditional security efforts focused on managing access, but new research by Onapsis and Flashpoint reveals an increase in cyber threats targeting SAP systems. Ransomware incidents have surged by 400%, and discussions about SAP vulnerabilities on various web platforms have increased by 490% from 2021 to 2023. Patching remains a challenge due to the need to balance system availability with downtime. Onapsis emphasizes the importance of integrating SAP into existing security programs, conducting regular vulnerability assessments, applying security patches promptly, and maintaining continuous security monitoring. Additionally, a secure development lifecycle and robust threat intelligence are essential for protecting SAP applications from evolving threats.
Jul 10, 2024
Related

- RISE with SAP
- SAP ABAP
- SAP ABAP Test Cockpit
- SAP Application Development and Integration
- SAP Basis
- SAP CIO
- SAP Code Inspector
- SAP CyberSecurity
- SAP Data Security
- SAP Development Tools
- SAP DevOps
- SAP Digital Transformation
- SAP Disaster Recovery
- SAP ECC 6.0
- SAP ECC Migration
- SAP Enterprise Threat Detection
- SAP ERP
- SAP Fiori
- SAP Governance Risk and Compliance
- SAP GRC
- SAP Identity Management
- SAP Process Control
- SAP QA
- SAP Quality and Testing
- SAP Regulatory Compliance
- SAP S/4HANA
- SAP Security
- SAP SOX Compliance
- SAP UI5
- SAP Vulnerability Analysis
- Show More
Your request has been successfully sent