SAP GRC
What is SAP GRC?
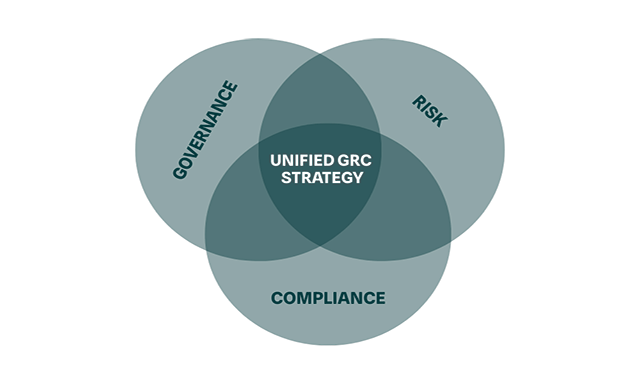
Governance, risk, and compliance (GRC) is a vital set of functions for enterprises to maintain secure and audit-friendly environments while being more confident in their actions. For SAP customers, SAP GRC can mean a set of GRC products provided by SAP itself or the GRC activities and technologies related to SAP systems.
What is SAP GRC?
Governance, risk, and compliance (GRC) is a vital set of functions for enterprises to maintain secure and audit-friendly environments while being more confident in their actions. For SAP customers, SAP GRC can mean a set of GRC products provided by SAP itself or the GRC activities and technologies related to SAP systems.
GRC is growing in importance with rapidly changing regulations that create new compliance challenges. Security and financial risks are also on the rise as companies adopt more cloud technologies, enact bring-your-own-device policies, and enable remote workers in greater numbers.
SAP GRC tools are available to help with areas of risk management, process control, financial compliance, threat detection, identity management, privacy governance, and more. SAP partners and other vendors that provide GRC solutions and consulting services include Appsian Security, Fastpath, and Soterion.
Key Considerations for SAPinsiders:
- Take inventory of your GRC processes and automate wherever possible. In our most recent GRC State of the Market research, successful GRC organizations are focused on automation to streamline processes. To do this, processes being automated need to be repeatable and effective. Before investing in GRC automation technology, it’s best to get processes in line. Many companies are automating the process of keeping track of who makes changes to the SAP systems.
- Digital transformation offers the opportunity to rethink GRC processes. If your company is implementing new software such as SAP S/4HANA, it’s smart to use that project as a catalyst to examine key GRC processes and find out how they can be improved. For example, HP set up a new GRC system during its SAP S/4HANA migration, including rethinking its user access processes and segregation of duties (SoD) ruleset. In the past HP relied on a homegrown tool for access control but implemented SAP Access Control and SAP Process Control as a component of its SAP S/4HANA migration.
- Determine the present and future state of remote work at your company, and how that impacts risk and security. Many companies have gone more remote in the past two years. For GRC groups, this provides more challenges for user access and opens companies up to more cyber threats. Map out your remote working landscape and determine what processes and tools you have in place to reduce risk.