SAP Data Security
What Is Data Security?
Data security is the practice of protecting data from unauthorized access, corruption, or theft throughout its lifecycle. Data security includes every aspect of information security, from the physical security of hardware and storage devices to administrative and access controls and application security. It also includes putting in place specific controls, standard policies, and procedures to protect data from a range of threats.
What Is SAP Data Security?
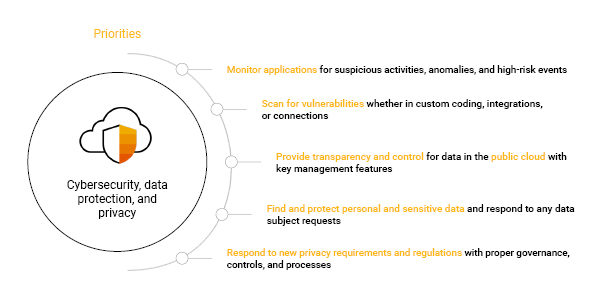
SAP security for the intelligence enterprise falls into four categories: identity and access governance, data protection and privacy, cybersecurity, and enterprise risk and compliance. In the data protection and privacy area, SAP has implemented a wide range of measures to help protect data controlled by SAP and its customers. These measures include:
What Is Data Security?
Data security is the practice of protecting data from unauthorized access, corruption, or theft throughout its lifecycle. Data security includes every aspect of information security, from the physical security of hardware and storage devices to administrative and access controls and application security. It also includes putting in place specific controls, standard policies, and procedures to protect data from a range of threats.
What Is SAP Data Security?
SAP security for the intelligence enterprise falls into four categories: identity and access governance, data protection and privacy, cybersecurity, and enterprise risk and compliance. In the data protection and privacy area, SAP has implemented a wide range of measures to help protect data controlled by SAP and its customers. These measures include:
- Data Processing Agreements: SAP signs data processing agreements with its cloud services provider, which mirror the terms of SAP’s customer-facing data protection agreement and include standard contractual clauses (SCCs). SAP implements and maintains technical and organizational measures to adequately protect personal data.
- Data Transfer Impact Assessments: SAP publishes FAQs to support customers with questions related to data transfer impact assessments when they are using SAP Cloud services.
- Data Protection Management System: The SAP data protection management system uses SAP’s data protection controls framework for all internal data protection and privacy controls, which cover the requirements of international industry standards.
- Internal Data Protection: SAP regularly trains employees and ensures data protection compliance with regular audits on the business and legal entity levels.
Further Resources for SAPinsiders
10 Best Practices for Enforcing Data Security, Control, and Consistency in the Software Logistics Process. In this article, security architect Kehinde Eseyin provides best practices, tips, and guidelines for ensuring that the process of making changes and transporting changed data in the SAP ABAP system is well secured against possible security threats and risks.
A Holistic Approach to Managing Cybersecurity & Protecting Your Data. This article provides tips and best practices to secure your data in the intelligent enterprise. SAP offers nearly a dozen solutions employed by many organizations — including SAP itself — to respond to compliance and security requirements and, in the event of a breach, minimize the impact, relates Bruce Romney, Senior Director of Product Marketing for SAP Governance, Risk and Compliance (GRC) and Security Solutions.
Overview of SAP Cybersecurity and Data Protection Solutions. In this presentation, Arndt Lingscheid, Global Solution Owner Cybersecurity and Data Protection at SAP SE, details steps organizations can take to secure the SAP S/4HANA business application environment.
Vendors that can assist SAP customers with data security include: Appsian Security, Capgemini, Fastpath, HPE, Intel, Kyriba, Layer Seven Security, NetApp, Onapsis, Rackspace, Saviynt, Security Weaver, Thales, Virtustream, Xiting, and Xpandion.