Step-by-Step Guide to Automating Your Invoice ProcessingThis e-book explains the drawbacks of manual invoice processing and provides a step-by-step guide to automating AP workflows with CIP, covering hidden costs, key KPIs, implementation steps, solution selection, ERP integration, real-world results, and the path to touchless invoicing.
Apr 28, 2026
•1 minute read
CVE-2026-23226: How a Missing Lock in ksmbd’s Channel List Exposes Your Linux SMB3 ServerThe Orca Security Research Pod identified a use-after-free race condition in the Linux kernel’s ksmbd SMB3 server that could allow an attacker with valid SMB credentials to exploit the system, leading to potential kernel panic or key exposure; a fix has been merged in kernel commit e4a8a96a93d, necessitating kernel updates.
Apr 20, 2026
•13 minute read
SACR Report: The Convergence of AI and Data SecurityThe SACR report highlights Orca Security's innovative advancements in the Unified Agentic Defense Platform, showcasing its agentless SideScanning technology to effectively manage Shadow AI and streamline visibility and governance across various cloud environments.
Apr 20, 2026
•1 minute read
The Unsteady Foundation of Traditional Identity GovernanceThis ebook exposes how years of patches, point tools, and “good enough” identity governance have left many organizations with a wobbling Jenga tower of access risk. It then shows why a converged, cloud-native identity security platform is the key to replacing that unsteady stack with a resilient foundation built for modern, AI-driven enterprises.
Apr 10, 2026
•2 minute read
Enabling Business With Modern Identity SecurityThis ebook shows how to break free from legacy identity tools and sunk-cost thinking so you can build a modern, cloud-native identity security foundation that actually accelerates the business instead of holding it back. By combining expert guidance, real-world practitioner insights, and a pragmatic roadmap, it helps you design an IGA program that is stakeholder-centered, agile, and ready for AI-driven, hybrid enterprises.
Apr 10, 2026
•3 minute read
Best Practices for Selecting an SAP Licensing PackageUnderstanding SAP licensing options offers flexibility and aligns with business goals, requiring careful consideration of package types, deployment methods, and process flows to avoid over-licensing and prepare for future growth.
Mar 27, 2026
•1 minute read
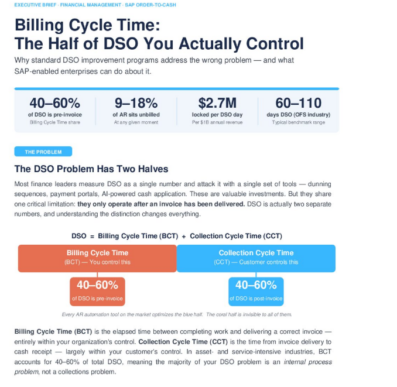
Unlocking Hidden Cash: Why Billing Cycle Time MattersBillions in earned revenue are sitting idle—not because customers aren’t paying, but because invoices aren’t going out fast enough. In complex SAP environments, unbilled work can quietly trap up to 18% of monthly revenue, inflating DSO and squeezing liquidity. The Hidden Cash Drain uncovers where these billing bottlenecks hide and how leading enterprises are regaining control of their cash flow. Download the full report to see how much working capital your organization could be leaving on the table.
Mar 12, 2026
•2 minute read
Billing Cycle Time: The Half of DSO You Actually ControlOrganizations often overlook that a significant portion of Days Sales Outstanding (DSO) happens before invoicing, emphasizing the importance of improving Billing Cycle Time (BCT) to enhance cash flow and operational efficiency.
Mar 12, 2026
•1 minute read
Your request has been successfully sent