Meet the Authors
Key Takeaways
-
SAP landscapes are shifting to hybrid and distributed models, necessitating integration modernization alongside continuous operations to minimize downtime and security risks, impacting SAP platform owners effectively.
-
The Jaguar Land Rover cyber incident underscores the importance of proactive security measures, revealing that without a robust integration and operational strategy, organizations face significant financial losses and operational disruptions.
-
Adopting a standardized Linux and automation stack enhances operational efficiency, reduces costs and transforms SAP teams' roles from manual tasks to managing automation assets.
SAP landscapes are becoming more hybrid and distributed, yet most organizations still run mission-critical processes that cannot tolerate extended downtime or security failures. Integration modernization now has to happen alongside continuous operations, especially as teams move away from aging middleware and adopt SAP BTP and event-driven architectures, explained presenters Jim O’Donnell from Red Hat and Azizur Rahman from ZMAN Consulting in the SAPinsider Las Vegas presentation “Stable SAP Operations Through Simplified and Scalable Integration.”
How a Stable Runtime Changes Day-to-Day Operations
The stakes around operational readiness are clear. The session highlighted the Jaguar Land Rover cyber incident, where an unpatched vulnerability sat exposed for four months and ultimately forced a five-week shutdown of global plants, sending 33,000 workers home and contributing to an estimated $2.5 billion dollars in losses. The patch was available, but gaps in alerting, playbooks and automated remediation meant the window between “patch available” and “patch applied” never closed.
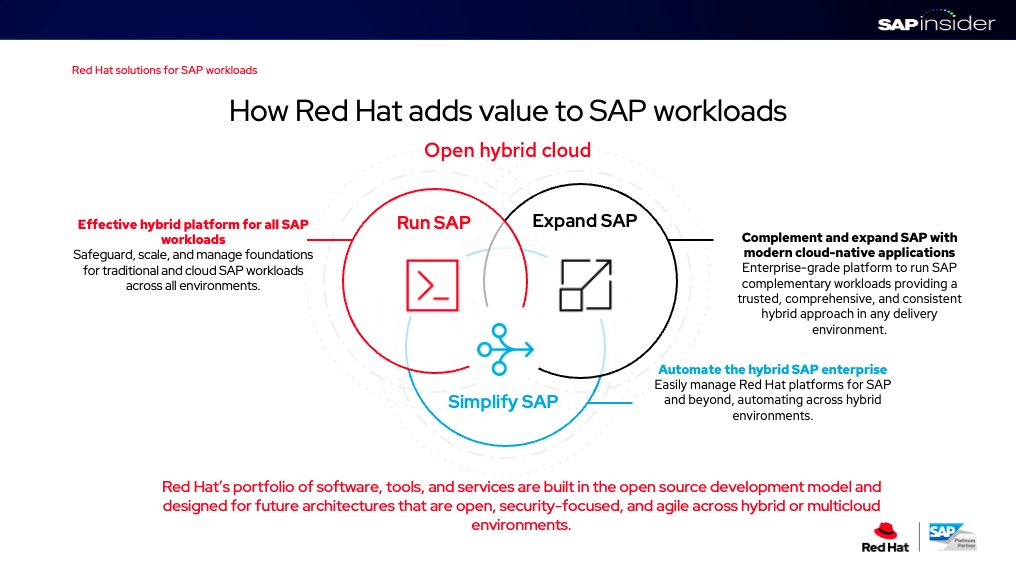
For SAP platform owners, that example reframes daily responsibilities. Instead of treating the operating system as a commodity, teams need an integrated platform that combines RHEL for SAP Solutions, centralized observability and Ansible-based remediation so security notes and CVEs translate into near-real-time action.
Explore related questions
Organizations that standardize on Red Hat Enterprise Linux have reported faster security updates, major reductions in unplanned downtime and significant improvements in mean time to repair, with multiyear ROI and short payback periods.
Integration modernization also affects day-to-day work for architects and integration leads. As companies shift from PI/PO-style middleware toward API- and event-driven patterns, responsibilities move from monolithic integration hubs into distributed runtimes at the edge and in Kubernetes-based platforms such as OpenShift. That change demands new operating disciplines, including shared decision templates for what runs where, edge patterns that keep the SAP core clean.
Ansible Automation Platform becomes central to this operating model. Research cited in the session showed that organizations using Ansible see substantial ROI, reduced unplanned downtime, and faster time to market for new products and services because routine Day 0-2 tasks are codified and reused across SAP systems. This changes daily work for SAP operations teams from hand-configuring hosts and performing ad hoc cutovers to maintaining a library of playbooks that handle provisioning, configuration, backups, upgrades and security policy enforcement across entire landscapes.

Developing a Strong Foundation For the Future
For technology executives evaluating integration and runtime platforms, the session outlined several criteria. Any foundation should provide a certified, jointly engineered base for SAP workloads with a long support lifecycle and coverage for heterogeneous on-premises and multicloud environments, reducing the need to maintain multiple operating environments in parallel.
Customer case studies illustrated the business impact of this approach. Organizations that standardized on a common Linux and automation stack for SAP reported hundreds of thousands of dollars in annual benefits per 100 virtual machines, driven by lower total cost of ownership, fewer outages and more efficient infrastructure teams.
Best practices for integration modernization included sequencing changes in phases. First, standardize the runtime and automation layer to ensure all SAP hosts conform to a common baseline and policy set. Second, identify high-risk or high-friction integration points, such as PI/PO interfaces connected to manufacturing or finance, and use reusable checklists to decide whether to replatform, wrap with APIs, or replace using SAP BTP and edge integration patterns. Finally, use event-driven automation to reduce risk during migration and cutover, including automated rollbacks, configuration drift management, and self-healing actions when services fail.
For SAP operations and architecture teams, adopting these practices means that everyday work becomes more about managing automation assets, validating policies, and reviewing exception reports than manually executing operational tasks.
What This Means for SAPinsiders
Platform standardization becomes a security imperative. SAP leaders should treat OS, management, and automation choices as safety-critical decisions that directly influence downtime risk, cyber exposure and modernization readiness.
Automation-first operations reshape talent needs. Basis and infrastructure teams will pivot from manual administration toward designing, governing and reusing automation content that spans SAP and non-SAP systems across hybrid environments.
Integration modernization demands phased, policy-led execution. Enterprise architects must pair edge and BTP patterns with reusable decision templates to upgrade integrations while preserving clean-core principles and business continuity.